最高-最新のSC-200資格認証攻略試験-試験の準備方法SC-200学習範囲
最高-最新のSC-200資格認証攻略試験-試験の準備方法SC-200学習範囲
P.S. PassTestがGoogle Driveで共有している無料かつ新しいSC-200ダンプ:https://drive.google.com/open?id=11R5GsGe4y6QemyalbjaTVXbbHuccr290
人生は勝ち負けじゃない、負けたって言わない人が勝ちなのよ。近年Microsoft SC-200認定試験の難度で大方の受験生は試験に合格しなかったのに面して、勇者のようにこのチャレンジをやってますか。それで、我々社のMicrosoft SC-200無料の試験問題集サンプルを参考します。自分の相応しい復習問題集バージョン(PDF版、ソフト版を、オンライン版)を選んで、ただ学習教材を勉強し、正確の答えを覚えるだけ、Microsoft SC-200資格認定試験に一度で合格できます。
SC-200試験は、Microsoft 365 Defender、Azure Defender、Azure SentinelなどのMicrosoft製品やサービスと協力するセキュリティオペレーションの専門家を対象としています。この試験では、これらの製品に対する候補者の理解と、セキュリティインシデントの検出と対応にどのように使用できるかを測定します。この試験では、セキュリティイベント管理、セキュリティインシデント対応、セキュリティガバナンスなどのセキュリティ運用概念に関する候補者の知識もテストします。
Microsoft SC-200認定試験は、キャリアを進めたいセキュリティプロフェッショナルにとって貴重な資格です。認定は、セキュリティオペレーションにおけるあなたのスキルと知識を検証し、フィールドでの求人機会においてより魅力的な候補者になります。さらに、認定は、最新のセキュリティのベストプラクティスと手法に常に精通していることを示し、認定されたセキュリティプロフェッショナルは、組織のセキュリティポジションを守るために必要なスキルと知識を持っている可能性が高いことを雇用主が知っています。
Microsoft SC-200 はこれで決まり
SC-200学習ガイドは、99%以上の合格保証をPassTest提供します。 そして、他のお客様と同じようにSC-200試験に合格すると信じています。 同時に、学習を続けたい場合は、SC-200ガイドトレントが1年以内の無料アップデートと1年以上の割引のメリットを提供します。 それまでの間、古い顧客として、他の対象テスト製品を購入するか、既存のSC-200学習テストを更新し続けるかどうかにより多くのメリットをMicrosoft Security Operations Analyst享受できます。
Microsoft Security Operations Analyst 認定 SC-200 試験問題 (Q82-Q87):
質問 # 82
You need to create a query for a workbook. The query must meet the following requirements:
List all incidents by incident number.
Only include the most recent log for each incident.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
正解:
解説:
Reference:
https://www.drware.com/whats-new-soc-operational-metrics-now-available-in-sentinel/
質問 # 83
You have a Microsoft Sentinel workspace
You develop a custom Advanced Security information Model (ASIM) parser named Parser1 that produces a schema named Schema1.
You need to validate Schema1.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
正解:
解説:
Explanation
Topic 2, Contoso Ltd
Case study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the button to return to the question.
Overview
A company named Contoso Ltd. has a main office and five branch offices located throughout North America.
The main office is in Seattle. The branch offices are in Toronto, Miami, Houston, Los Angeles, and Vancouver.
Contoso has a subsidiary named Fabrikam, Ltd. that has offices in New York and San Francisco.
Existing Environment
End-User Environment
All users at Contoso use Windows 10 devices. Each user is licensed for Microsoft 365. In addition, iOS devices are distributed to the members of the sales team at Contoso.
Cloud and Hybrid Infrastructure
All Contoso applications are deployed to Azure.
You enable Microsoft Cloud App Security.
Contoso and Fabrikam have different Azure Active Directory (Azure AD) tenants. Fabrikam recently purchased an Azure subscription and enabled Azure Defender for all supported resource types.
Current Problems
The security team at Contoso receives a large number of cybersecurity alerts. The security team spends too much time identifying which cybersecurity alerts are legitimate threats, and which are not.
The Contoso sales team uses only iOS devices. The sales team members exchange files with customers by using a variety of third-party tools. In the past, the sales team experienced various attacks on their devices.
The marketing team at Contoso has several Microsoft SharePoint Online sites for collaborating with external vendors. The marketing team has had several incidents in which vendors uploaded files that contain malware.
The executive team at Contoso suspects a security breach. The executive team requests that you identify which files had more than five activities during the past 48 hours, including data access, download, or deletion for Microsoft Cloud App Security-protected applications.
Requirements
Planned Changes
Contoso plans to integrate the security operations of both companies and manage all security operations centrally.
Technical Requirements
Contoso identifies the following technical requirements:
Receive alerts if an Azure virtual machine is under brute force attack.
Use Azure Sentinel to reduce organizational risk by rapidly remediating active attacks on the environment.
Implement Azure Sentinel queries that correlate data across the Azure AD tenants of Contoso and Fabrikam.
Develop a procedure to remediate Azure Defender for Key Vault alerts for Fabrikam in case of external attackers and a potential compromise of its own Azure AD applications.
Identify all cases of users who failed to sign in to an Azure resource for the first time from a given country. A junior security administrator provides you with the following incomplete query.
BehaviorAnalytics
| where ActivityType == "FailedLogOn"
| where ________ == True
質問 # 84
You have a Microsoft subscription that has Microsoft Defender for Cloud enabled You configure the Azure logic apps shown in the following table.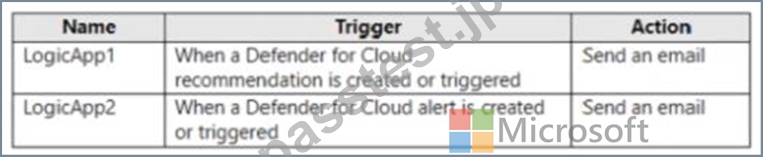
You need to configure an automatic action that will run if a Suspicious process executed alert is triggered. The solution must minimize administrative effort.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.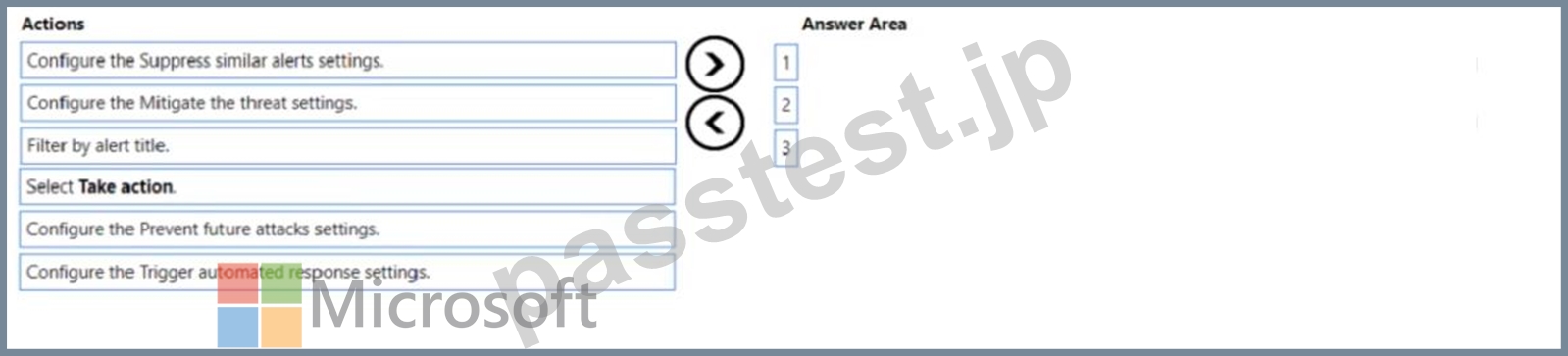
正解:
解説: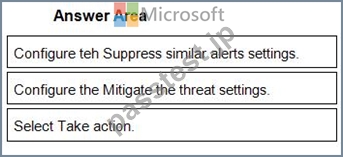
1 - Configure teh Suppress similar alerts settings.
2 - Configure the Mitigate the threat settings.
3 - Select Take action.
質問 # 85
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
正解:
解説:
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/bookmarks
質問 # 86
You have the following advanced hunting query in Microsoft 365 Defender.
You need to receive an alert when any process disables System Restore on a device managed by Microsoft Defender during the last 24 hours.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. Add | order by Timestamp to the query.
- B. Block DeviceProcessEvents with DeviceNetworkEvents.
- C. Create a detection rule.
- D. Add DeviceId and ReportId to the output of the query.
- E. Create a suppression rule.
正解:C、D
解説:
Reference:
https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/custom-detection- rules
Topic 1, Litware inc.
Overview
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
Overview
Litware Inc. is a renewable company.
Litware has offices in Boston and Seattle. Litware also has remote users located across the United States. To access Litware resources, including cloud resources, the remote users establish a VPN connection to either office.
Existing Environment
Identity Environment
The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com.
Microsoft 365 Environment
Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled.
Azure Environment
Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table.
Network Environment
Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription.
On-premises Environment
The on-premises network contains the computers shown in the following table.
Current problems
Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously.
Planned Changes
Litware plans to implement the following changes:
Create and configure Azure Sentinel in the Azure subscription.
Validate Azure Sentinel functionality by using Azure AD test user accounts.
Business Requirements
Litware identifies the following business requirements:
Azure Information Protection Requirements
All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection - Data discovery dashboard.
Microsoft Defender for Endpoint Requirements
All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint.
Microsoft Cloud App Security Requirements
Cloud App Security must identify whether a user connection is anomalous based on tenant-level data.
Azure Defender Requirements
All servers must send logs to the same Log Analytics workspace.
Azure Sentinel Requirements
Litware must meet the following Azure Sentinel requirements:
Integrate Azure Sentinel and Cloud App Security.
Ensure that a user named admin1 can configure Azure Sentinel playbooks.
Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook.
Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting.
Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account.
質問 # 87
......
PassTestのITの専門研究者はMicrosoft SC-200認証試験の問題と解答を研究して、彼らはあなたにとても有効な訓練試験オンラインサービスツールを提供します。もしあなたはPassTestの製品を購入したければ弊社が詳しい問題集を提供して、君にとって完全に準備します。弊社のPassTest商品を安心に選択してPassTest試験に100%合格しましょう。
SC-200学習範囲: https://www.passtest.jp/Microsoft/SC-200-shiken.html
- SC-200模試エンジン ???? SC-200全真模擬試験 ???? SC-200最新試験 ???? ▷ www.goshiken.com ◁サイトにて最新➥ SC-200 ????問題集をダウンロードSC-200最新試験
- SC-200資格認定試験 ???? SC-200学習資料 ???? SC-200テスト内容 ???? サイト【 www.goshiken.com 】で{ SC-200 }問題集をダウンロードSC-200最新対策問題
- SC-200資格認証攻略を利用して、Microsoft Security Operations Analystをパスします ???? 今すぐ➥ www.goshiken.com ????で《 SC-200 》を検索し、無料でダウンロードしてくださいSC-200最新試験
- SC-200問題トレーリング ???? SC-200テスト内容 ???? SC-200専門試験 ???? 【 www.goshiken.com 】に移動し、▷ SC-200 ◁を検索して、無料でダウンロード可能な試験資料を探しますSC-200受験記対策
- 100%合格率SC-200|効率的なSC-200資格認証攻略試験|試験の準備方法Microsoft Security Operations Analyst学習範囲 ???? サイト➡ www.goshiken.com ️⬅️で☀ SC-200 ️☀️問題集をダウンロードSC-200日本語復習赤本
- SC-200資格認証攻略を利用して、Microsoft Security Operations Analystをパスします ???? 時間限定無料で使える▛ SC-200 ▟の試験問題は⮆ www.goshiken.com ⮄サイトで検索SC-200日本語版対策ガイド
- ハイパスレートのSC-200資格認証攻略一回合格-一番優秀なSC-200学習範囲 ???? 今すぐ➠ www.goshiken.com ????で( SC-200 )を検索して、無料でダウンロードしてくださいSC-200最新試験
- SC-200資格認証攻略を利用して、Microsoft Security Operations Analystをパスします ???? ( www.goshiken.com )で☀ SC-200 ️☀️を検索して、無料でダウンロードしてくださいSC-200最新対策問題
- SC-200資格認定試験 〰 SC-200出題内容 ???? SC-200最新対策問題 ???? ☀ www.goshiken.com ️☀️を入力して➥ SC-200 ????を検索し、無料でダウンロードしてくださいSC-200出題内容
- SC-200問題トレーリング ???? SC-200学習資料 ???? SC-200問題トレーリング ???? 最新➤ SC-200 ⮘問題集ファイルは{ www.goshiken.com }にて検索SC-200学習資料
- 初心者でも合格できる!SC-200 試験問題 ???? { www.goshiken.com }の無料ダウンロード▶ SC-200 ◀ページが開きますSC-200最新対策問題
P.S. PassTestがGoogle Driveで共有している無料かつ新しいSC-200ダンプ:https://drive.google.com/open?id=11R5GsGe4y6QemyalbjaTVXbbHuccr290
What's Your Reaction?




![Noots Focus Reviews [Truth Exposed 2025]!](https://news.bangboxonline.com/uploads/images/202501/image_430x256_678e3b94881a1.jpg)
![Vivalis Male Enhancement: The Must-Know Ingredients [2025 Update]](https://news.bangboxonline.com/uploads/images/202501/image_430x256_678e3b54e396c.jpg)






